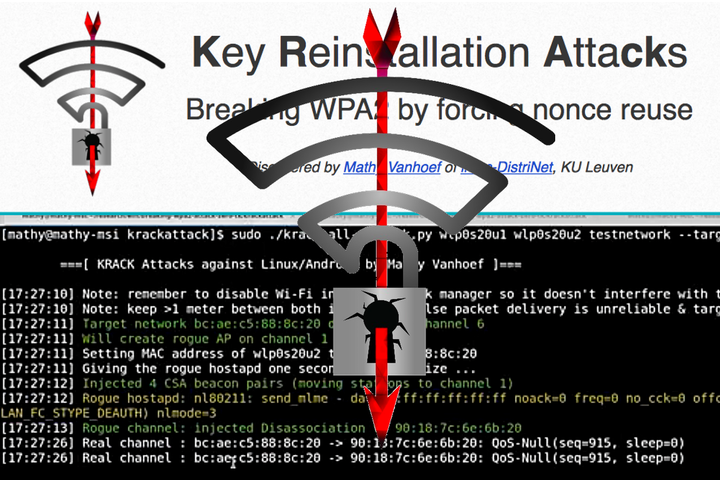
KRACK attack on WPA 2 Router Configuration
When a vulnerability that can compromise the security of anyone using a Wi-Fi connection, IT pros tend to take notice.
In case you slept in late this Monday, here’s a quick refresher of the WPA2 KRACK attack — and some insights about how to address it.
What is the WPA2 KRACK attack?
The bug was discovered by Mathy Vanhoef of Belgian university KU Leuven. Vanhoef created this website to explain what he is calling the KRACK attacks. According to the site:
“We discovered serious weaknesses in WPA2, a protocol that secures all modern protected Wi-Fi networks. An attacker within range of a victim can exploit these weaknesses using key reinstallation attacks (KRACKs). Concretely, attackers can use this novel attack technique to read information that was previously assumed to be safely encrypted. This can be abused to steal sensitive information such as credit card numbers, passwords, chat messages, emails, photos, and so on. The attack works against all modern protected Wi-Fi networks. Depending on the network configuration, it is also possible to inject and manipulate data. For example, an attacker might be able to inject ransomware or other malware into websites.
“The weaknesses are in the Wi-Fi standard itself, and not in individual products or implementations. Therefore, any correct implementation of WPA2 is likely affected. To prevent the attack, users must update affected products as soon as security updates become available. Note that if your device supports Wi-Fi, it is most likely affected. During our initial research, we discovered ourselves that Android, Linux, Apple, Windows, OpenBSD, MediaTek, Linksys, and others, are all affected by some variant of the attacks. For more information about specific products, consult the database of CERT/CC, or contact your vendor.”
What now? Steps you should take to deal with the WPA2 vulnerability
So what should IT pros do about the KRACK attacks? It all comes down to fixing what you can, being cautious, and using common sense.
Patrick Monroe, GM/CEO at Austin-based TC Tech Systems said that this bug is similar to many bugs that came before it, while also being totally different at the same time.
“Generally, when a hack is developed it exposes some vulnerability in the protocol, which is what happened here,” he said. “But this is different in that WPA2 is more robust than earlier versions, yet they’ve managed to expose a vulnerability in its algorithm,” a development that’s troubling to say the least.
“(WPA2) is often perceived as generally secure,” he added about the ubiquitous protocol. “So it’s different in the sense that such a well-known and trusted security measure has been compromised.”
Monroe said his firm will do the same thing he would tell a client or another IT pro to do. He said that it’s obviously important to wait and see how the industry responds over the next few days. But in the meantime, he suggested minimizing exposure by avoiding Wi-Fi when possible. He noted that most entities use Wi-Fi, but usually have other options at their disposal.
“In the interim, I would use discretion about using Wi-Fi when possible, especially in a public setting,” he said.
Where to find the latest updates
While fixes to the WPA2 issue are forthcoming, not every vendor currently has a fix. As a result, it might take some time before you’re able to patch your entire environment.
Until then, it might be in your best interest to disconnect from Wi-Fi if you are dealing with sensitive data and use other means of connecting to networks until you can fully patch your OSes, devices, and networking gear. Also, the following continuously updated lists will keep you informed on the latest:
- List of companies affected by the WPA2 vulnerability
- Current status of the WPA2 patches released by vendor
- Spiceworks resource page about the WPA2 KRACK attacks
What steps, if any, are you taking to protect your organization from the WPA2 security flaw? Let us know in the comments below.
Source: Spice Works

0 comments